Capabilities
Strategic Resilience & Institutional Precision.
Advisory services are structured to address the complexities of modern global risk through the lens of the 'Clean Space'. Engagement is reserved strictly for principals and family offices requiring sophisticated, bespoke oversight rather than strand security templates. By prioritising intelligence -led design and jurisdictional privacy, the firm ensures that every protective framework is as discreet as it is impenetrable.

Risk Architecture & Framework Design
Standard security templates are discarded in favor of a designed, underlying architecture for the Principal's protective environment. This process involves the development of private operating protocols, the vetting of third-party vendors, and the seamless integration of security for primary residences, family estates, and maritime assets. The objective is a system where safety remains a background constant rather than an intrusive presence.
Cross-Border Advisory & Global Oversight
Raw information is a liability; only actionable intelligence provides security. We maintain oversight across the physical, digital & reputational variables that define a Principal's standing. Through predictive modeling and real-time analysis, we identify emerging threats in high-stakes jurisdictions before they manifest - prioritizing strategic avoidance over tactical reaction.


Family Office Continuity & Asset Resilience
Resilience is the baseline for any enduring legacy. We synchronize the space between physical security, legal counsel & estate management to guarantee that administrative and operational functions remain uninterrupted during a crisis. This integrated oversight provides total continuity - securing both the long-term legacy and the immediate family estate.
Technical & Digital Counter-Measures
The preservation of "Clean Space" is achieved through rigorous, specialized oversight. This includes Technical Surveillance Counter-Measures (TSCM) to identify and eliminate illicit monitoring, alongside the aggressive auditing of digital signatures. Private and professional environments are rendered impenetrable to unauthorized data collection or tracking.


Digital Information Security & Counter-Intelligence
Standard cybersecurity is replaced by an aggressive stance on digital defense. Operations prioritize the securing of private communication channels, the hardened encryption of personal networks, and the proactive monitoring of the deep web for leaked credentials or compromised assets. Through continuous auditing of the Principal and their inner circle, vulnerabilities are precluded before they can be exploited for financial or reputational leverage.
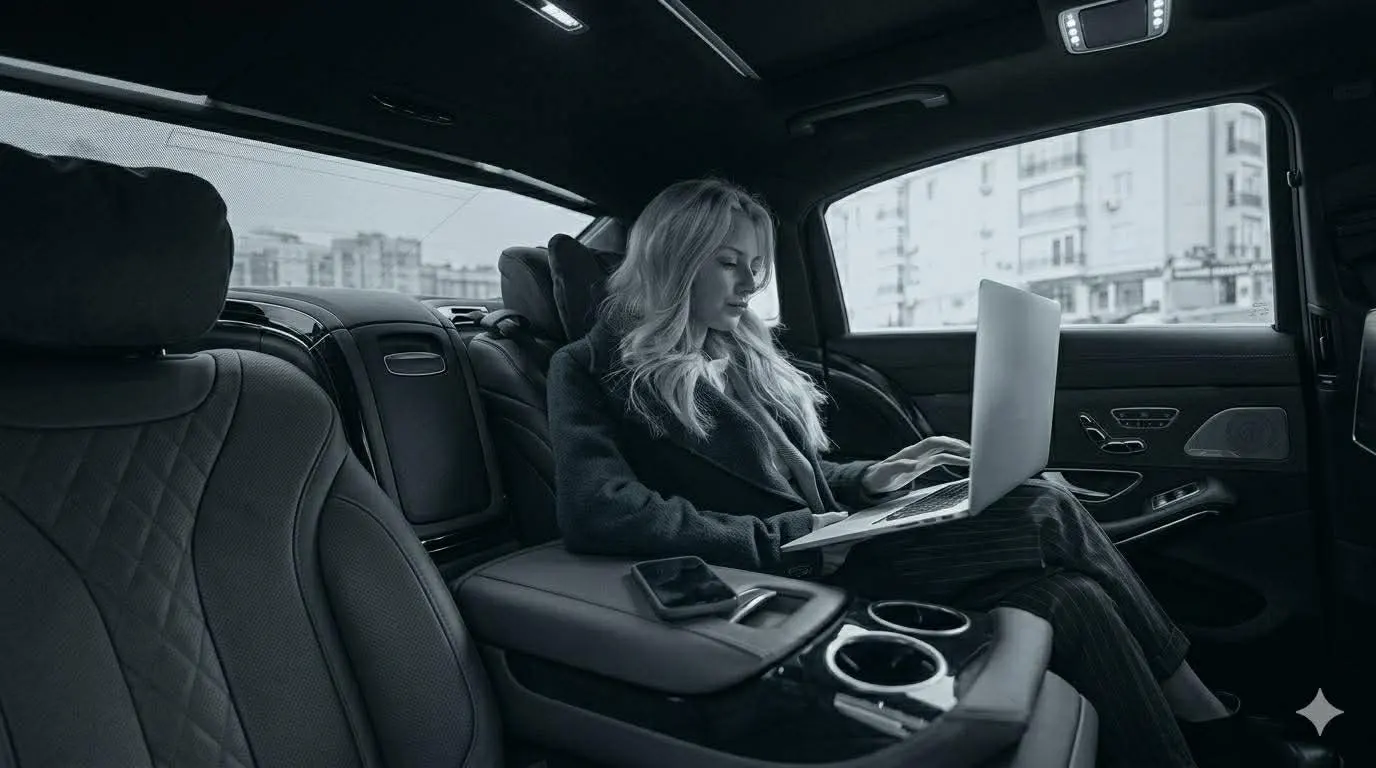
Travel Risk Intelligence & Global Oversight
Advanced intelligence dictates all international movements within high-risk or complex jurisdictions. Operations prioritize the vetting of local air and ground transport, secure lodging audits, and the enforcement of "Safe Passage" protocols. The result is a Principal insulated from operational friction and local instability, while maintaining a minimal signature.

Reputational Resilience & Brand Protection
Threats to a Principal's public standing or professional legacy are precluded at the source. Operations prioritize the command of the "Information Environment" - addressing latent vulnerabilities, auditing the digital footprints of family members, and enforcing privacy frameworks that preempt the exploitation of personal data by external actors.
Kidnap, Ransom & Extortion Advisory (KRE)
Preventative frameworks and performance-tested protocols address the reality of kidnapping and extortion threats "Left of Bang" strategies - identifying vulnerabilities in daily routines or digital presences before they can be exploited. Technical precision and discreet communication protocols govern the response to any manifested threat.

